In the vast and often concealed corners of the internet, specialized marketplaces have emerged that offer access to high-value digital commodities. Among these, BClub stands out as a well-known platform, particularly for bclub its premium inventory of financial data, often referred to as “dumps” in cybersecurity circles. Accessing BClub’s premium inventory is not as simple as creating a standard account—it requires a verified entry point, an exclusive process that ensures security, trust, and anonymity for its users. This blog explores the verified entry point of BClub, the nature of its premium inventory, and the broader lessons that can be learned from this hidden ecosystem.
Understanding BClub and Its Premium Inventory
BClub is part of a larger ecosystem of dark web marketplaces where sensitive data, including credit card information and financial profiles, is bought and sold. Its premium inventory is distinguished by the quality and completeness of the data it offers. Premium dumps include full credit card details—numbers, expiration dates, CVV codes, and sometimes additional personal information such as cardholder names and addresses. These data sets are in high demand because of their reliability and immediate usability in illicit transactions.
The concept of “premium inventory” is central to BClub’s reputation. While lower-tier dumps may be incomplete or outdated, the premium inventory guarantees verified, high-quality data. This exclusivity makes access highly controlled and underscores the platform’s focus on trustworthiness and professionalism, even in a criminal context.
The Concept of a Verified Entry Point
Unlike conventional websites, BClub does not allow open registration. The platform operates with a verified entry point—a controlled access system designed to prevent infiltration by law enforcement, scammers, or malicious actors. This entry point serves multiple purposes:
- Security: By restricting access, BClub reduces the risk of unauthorized intrusion, protecting both the platform and its users.
- Trust: Users who gain entry are generally vetted or referred by existing members, creating a semi-private community where trust is easier to establish.
- Quality Control: Limiting access ensures that only serious participants interact with the premium inventory, maintaining the integrity and reputation of the platform.
The verified entry point is thus not merely a login page; it is a gatekeeper that safeguards the marketplace, its vendors, and its high-value inventory.
How Logging In Works
While the exact mechanics of logging into BClub’s premium inventory are confidential, cybersecurity research and reports from dark web investigations provide some insights:
- Invitation or Referral System: Many users gain access through invitations from existing members, ensuring that new entrants are known entities or have trusted connections.
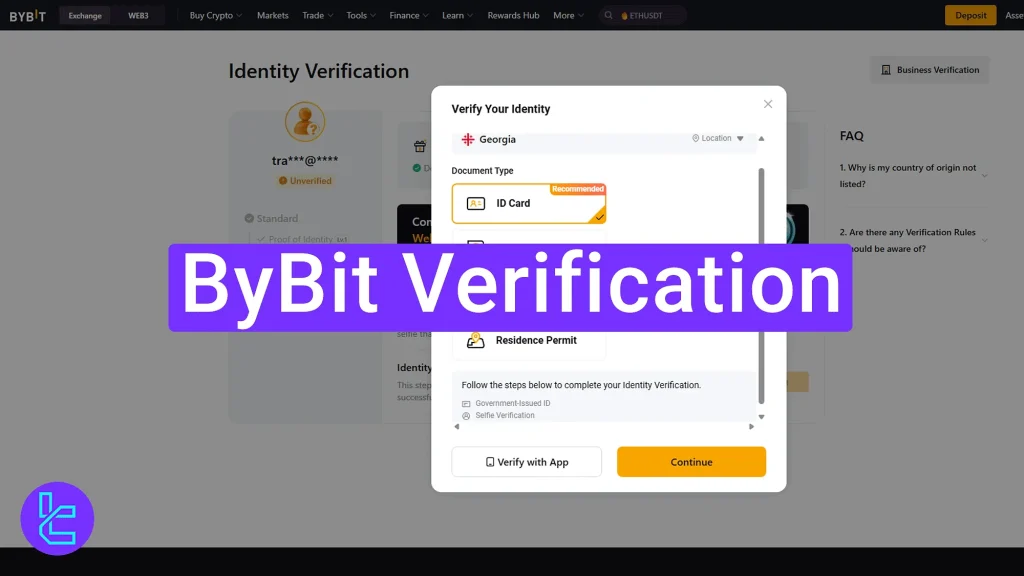
- Multi-Step Verification: Potential users often undergo a verification process, which may include identity checks, digital proofs of previous transactions on similar platforms, or other vetting mechanisms.
- Anonymity Protocols: Access requires using secure networks such as Tor or VPNs, along with pseudonymous accounts. These measures prevent the exposure of real-world identities and protect against surveillance.
- Secure Authentication: Two-factor authentication and other cryptographic methods are often employed to enhance account security and prevent unauthorized access.
This multi-layered approach ensures that logging in is not just about entering credentials but is part of a broader security ecosystem designed to protect the platform and its premium inventory.
Exploring the Premium Inventory
Once logged in, users can navigate BClub’s premium inventory, which is organized to maximize usability and efficiency.
Detailed Listings
Each entry in the premium inventory includes comprehensive information about the financial data available. This typically consists of card type, issuing bank, cardholder details, and sometimes geographic information. Such thorough descriptions help buyers make informed decisions while minimizing the risk of acquiring unusable data.
Vendor Reputation
BClub emphasizes reliability by integrating vendor reputation systems. High-rated sellers are more likely to have bclub login repeat business, and their listings are prioritized. This rating system encourages vendors to maintain high-quality standards, fostering trust even within an illicit marketplace.
Secure Transactions
Transactions within BClub’s premium inventory are often conducted through secure payment systems and escrow services. Funds are held until buyers confirm receipt of valid data, mitigating the risk of fraud and ensuring that both parties are protected despite the illegal nature of the marketplace.
User Experience
Despite the illegal focus, BClub has invested in user experience. The inventory is organized with categories, filters, and search functions, enabling users to quickly find the data they need. The platform balances discretion with usability, reflecting a professional approach to dark web commerce.
Risks and Consequences
Engaging with BClub’s premium inventory carries severe legal, ethical, and personal risks. Buyers and sellers risk criminal prosecution, financial penalties, and long-term consequences if caught. There is also the danger of exposure to malware, scams, and other cyber threats.
Beyond individual consequences, the operation of platforms like BClub contributes to broader societal harms, including identity theft, financial fraud, and erosion of trust in digital financial systems. Ethically, while anonymity tools can protect legitimate privacy interests, their exploitation for criminal activity demonstrates the potential dangers of unregulated online spaces.
Lessons from BClub’s Verified Entry Point
Although BClub is an illegal marketplace, it provides important lessons in cybersecurity, digital behavior, and risk management:
- Importance of Cybersecurity: Protecting personal financial data is paramount. Strong passwords, two-factor authentication, and vigilant monitoring of accounts are essential defenses.
- Understanding Controlled Access: The verified entry point illustrates the role of access control in maintaining security and trust within digital ecosystems, even illicit ones.
- Digital Anonymity Risks: Platforms like BClub show that while anonymity can safeguard privacy, it also facilitates criminal activity, highlighting the double-edged nature of digital anonymity.
- Adaptability of Cybercriminals: The platform demonstrates that cybercriminals adapt to technological and legal challenges. Awareness and continuous learning are critical to staying ahead of evolving threats.
Conclusion
BClub’s premium inventory represents a highly organized, professionalized segment of the dark web. Accessing it through the verified entry point is more than a login process—it is an entry into a carefully managed ecosystem designed to protect high-value data, ensure trust, and facilitate secure transactions in an illegal market.
While the platform demonstrates sophistication and structure, the risks of engagement are substantial. Legal repercussions, ethical concerns, and the potential for financial or digital harm make participation dangerous. However, understanding BClub’s operation and the concept of a verified entry point provides valuable insights into cybersecurity, digital literacy, and the complexities of online anonymity.
The story of BClub reminds us that the internet is a layered ecosystem. Beneath the visible surface, sophisticated networks operate with their own rules, risks, and structures. By studying these systems, individuals and organizations can better understand the importance of protecting digital information, recognizing threats, and navigating online spaces responsibly.
Beyond the login screen lies a complex world—one that is highly organized, potentially lucrative for criminals, and inherently dangerous. Awareness, caution, and strong cybersecurity practices are the keys to understanding and surviving the digital frontier.